Hybrid IT is the talk of the town – Cloud and On-Premises are coexisting and are being monitored, managed and utilized parallelly. The market is moving towards an era where technical transformation will be driven through a Hybrid approach. To harness this transformation, enterprises are required to manage multiple applications and identities that spans across on-premises […]
The current pandemic situation escalated ransomware and phishing scams, with cybercriminals taking advantage of insecure systems and networks, impacting both large and small businesses. In fact, the average cost of a data breach during the pandemic witnessed an increase to reach USD 21,659 per incident, with most incidents ranging from USD 826 to USD 653,587, […]
Regulatory compliances and IAM technology go hand-in-hand, as they focus on the same two entities—user and data. At a high level, it includes user’s actions around data, users’ accountability, user’s privacy and data protection. While IAM implementation is often believed to be a high expense task for organizations, it is also pegged as an investment—that […]
While a provisioning system enables enterprises to add, modify and delete user accounts on various business applications, it is also imperative for organizations to implement access parameters as per the business requirement. However, the challenge is to select the right access conditions and ensuring that employees are given only the appropriate amount of access to […]
The key to the management of identities, an agile Active Directory (AD) acts as a map between names and values. In comparison to native tools, it is easier and faster for addressing the auditing and security needs of an enterprise, along with ensuring workflow streamlining, providing business continuity and optimizing IT capabilities. In fact, the […]
The modern pandemic-era disrupted the business ecosystem drastically, with enterprises scouting for immediate digital transformation to accommodate the new normal of remote working. This provided an ‘appropriate’ moment for hackers and people with malicious intent to target vulnerable systems and networks, causing large-scale data breaches, ransomware and malware attacks. Enterprises, especially with minimal or inadequate […]
Access to the cloud for running business and managing applications has made life easier for organizations. Undoubtedly, the exceptionally convenient cloud environment helps you identify the data security risks and safely vault the confidential data. Cloud governance is adopted, managed, and regulated to enhance data security to address technical glitches or malicious attacks through identity […]
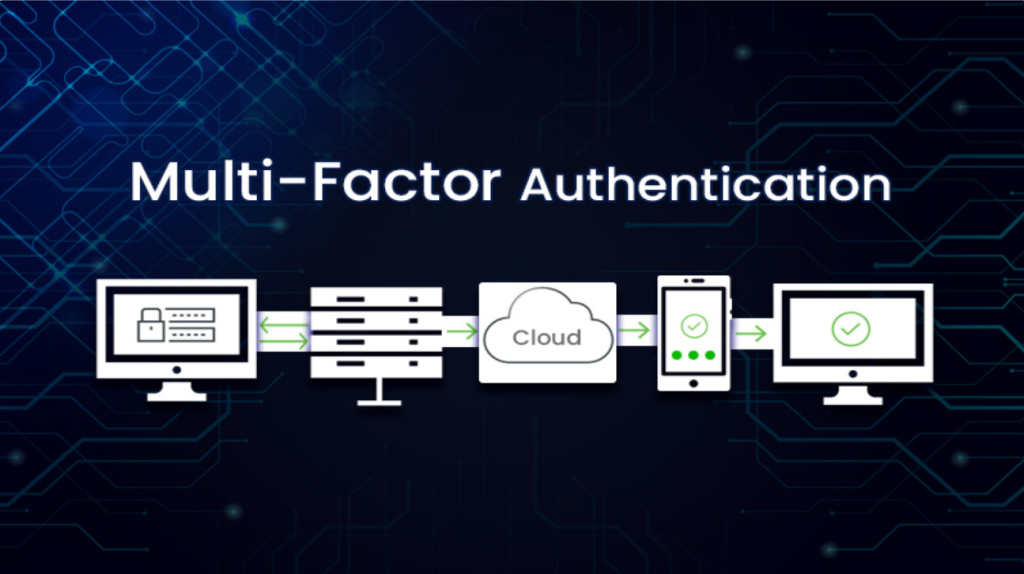
Despite being a necessity for identity security, IAM solutions also come with a number of challenges that include application distribution, fragmented workforce, issues with passwords, and many others. Further, increasing numbers of identities, data, and cybercrime have been overwhelming the traditional IAM systems, which have manual processes and rely on static data. Such systems have […]
According to Gartner, global expenditure by end-users on public cloud services is expected to increase by 21.7 per cent, reaching a total of USD 597.3 billion in 2023, compared to the USD 491 billion recorded in 2022 . Further, Gartner indicates that 75 per cent of organizations by 2026 will embrace a digital transformation approach […]
By their very nature, IT network of educational/ academic institutions are used by a large number of transient users. One of the examples of a transient user is an aspiring student who fills up an application and use parent’s credit card to make the payment. Such details are stored in the institution’s system. Academic institutions […]
Enterprises are increasingly facing application integration challenges with dynamic changes in their business requirements and IT ecosystem. With organizations focusing on implementing diverse applications for their varied needs, they are also prioritizing faster turn-around time and efficient integration systems. The challenge is to create an agile app onboarding process while maintaining the essential security posture, […]
As the world struggles to contain the current coronavirus onslaught, cybercriminals are implementing creative social engineering methods for accessing networks, systems, and passwords. Capitalizing on the fear and uncertainty of the situation, cybercriminals are exploiting a human weakness to tempt users into conducting insecure online behavior, leading to detrimental consequences in the present scenario. Cybercriminals […]
The key to the management of identities, an agile Active Directory (AD) acts as a map between names and values. In comparison to native tools, it is easier and faster for addressing the auditing and security needs of an enterprise, along with ensuring workflow streamlining, providing business continuity and optimizing IT capabilities. In fact, the […]
Irrespective of the industry you are catering to, Virtual Private Networks (VPN) are still used at large to meet the organizational IT ecosystem demands. These VPNs enable remote users to securely establish connection with the core IT infrastructure components, be it over on-prem setups or cloud infrastructure hosted with AWS or any other cloud provider. […]
Deploying IAM Managed Services have become a norm for enterprises to track and secure their business information, be it about their finances or employees and their identities. Being a business owner, your client needn’t bother about slogging stats and security features threatening to wreak havoc to their enterprise. IAM Managed Services are not child’s play, so business […]
Growing concerns of cybersecurity have left business owners in dilemma. 80% of organizations prioritize their privilege security and expressed how critical it is to maintain an isolated environment to ensure IT security. Protecting privileged assets and isolating environments within your IT security eco-system is still a tough task. Because, cyber attacks may occur anytime and ruin […]
With the world moving rapidly to digitization, the information collected and stored digitally is becoming vulnerable to cyber-attacks. As the cyber safety protocols and technologies including Identity and Access Management as well as Identity Governance are becoming advanced. They are stringently monitoring the information, and identities of enterprises from possible cyber-attacks. But the miscreants are […]
When it comes to managing the various aspects of a small enterprise, most technology providers put less efforts in that regard. But, solutions like Salesforce managed Services have made a difference to the age-old trend of focusing on large enterprises and taking care of small ventures as well. Being a popular application development Customer Relationship […]
Swift functioning of IAM systems is imperative for workflow operations, regulatory compliance and security requirements. Information security professionals grapple with the challenge of keeping IT system running, and ensuring that IAM capabilities are aligned to serve the business needs. One also has to ensure just right dependence on centralization and de-centralization for extending permissions, certifications […]
Before we move ahead let me break the biggest myth of present times – Serverless Applications is servers on cloud and are to be managed by the cloud server providers. The term “Serverless” Applications gives an idea that administration of servers, which is one of the biggest headaches for IT teams, is not required. At […]